Ransomware is more prominent, more sophisticated and more troublesome than ever. Hospitals, homeowners, consumers and corporations have all have made headlines this year as victims of malicious computer viruses. Designed to encrypt digital files and render them useless until you pay a hefty ransom, payments have now ballooned to an average of just under $150,000.
If you can believe it, the reality is even more dire. The average payment is so high because of a handful of seven figure payouts. But most payments are in the $50,000 range with hackers targeting small and medium businesses as well as individuals.
Carbonite has a solution to this problem, and it’s important to understand how our backup solutions protect you and your data against cybercriminals. If you take the initiative and protect your files with Carbonite before you’re hit with ransomware, you’ll never need to pay the ransom.
How Carbonite protects computers from ransomware
Carbonite’s versioning capabilities are the key to restoring desktop or laptop computer files that have been encrypted with ransomware. If you’re using a Carbonite home plan and your computer files get encrypted due to ransomware, you can simply use Carbonite to restore a version of the file that was backed up before the ransomware attack took place.
You will also need to remove the ransomware and delete all infected files before you start restoring clean versions. If your computer becomes infected with ransomware, take the following steps:
- Remove the computer from the network it’s running on so the infection doesn’t spread to other computers. If the computer isn’t running on a network, skip this step.
- Shut down the computer by holding down on the power button.
- Turn the computer back on and select Safe Mode with Networking.
- Reconnect to the Internet then download and run a malware detection and removal tool.
- Once the virus is removed, delete all encrypted files and restore clean versions from Carbonite’s cloud backup service.
If you run the anti-malware software and believe the computer is still infected, or if you have trouble booting your computer in Safe Mode with Networking, contact an IT professional to help you wipe the computer clean and remove the virus. Another option is to use Carbonite to restore your files to a new or different computer.
Important Note: As soon as your computer is virus-free, contact the Carbonite Customer Care Team and tell them what happened. They’ll be able to guide you through the process of restoring clean versions of your files. Carbonite’s award-winning, U.S.-based Customer Care Team is available seven days a week.
How Carbonite protects servers from ransomware
If you’re using a Carbonite Safe® Server backup product to protect the data on your company’s servers, you can restore previous versions of your files the same way Carbonite Home plan users can. But Carbonite Safe® Server backup has additional features that make the process of recovering from a ransomware attack fast and simple.
Specifically, with Carbonite Safe® Server backup, you have greater control over how many copies of your files Carbonite will save and how long they’ll be retained. This gives you more freedom and flexibility when it comes to determining a Recovery Point Objective (RPO), the point in time you need to go back to in order to retrieve clean versions of your files. For example, if you were attacked with ransomware two days ago, a safe RPO would be three days ago.
Carbonite Safe® Server backup plans also offer “hybrid” protection, which means that users can back data up to a server located on premises as well as to the cloud. Hybrid backup is considered an industry best practice for businesses because it combines the speed and convenience of local backup and recovery with the extra protection of the cloud. With hybrid backup, if your local server becomes damaged or unusable, you’ll still have a copy of your files stored safely in the cloud.
Carbonite Safe® Server backup plans allow users to configure a separate retention policy for backups stored locally and backups stored in the cloud. To configure retention settings for local and cloud backup, simply navigate to the Retention settings section and make your selections.
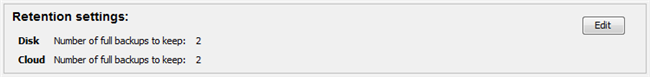
Retaining past backups allows for quick and easy recovery from ransomware and other malicious computer viruses.
The only way a backup copy is removed is if the retention policy you set expires, or if you manually delete it. Every backup is added to a disk or the cloud without overwriting previous backups. Of course, it’s crucial to set a retention policy that meets your needs and stays within your allotted budget.
Learn more about Carbonite Home plans and Carbonite Safe® Server backup today.










